A Strategic Governance and Risk Architecture
A Strategic Governance and Risk Architecture
Principles of Information Security Management
1. Security and Risk Management (1 - 2h)
1. Security and Risk Management (1 - 2h)
3. Security Architecture and Engineering (3 - 4 hrs)
3. Security Architecture and Engineering (3 - 4 hrs)
4 - Communication and Network Security (2 - 3 hrs)
4 - Communication and Network Security (2 - 3 hrs)
5 - Identity and Access Management (1- 2hr)
5 - Identity and Access Management (1- 2hr)
1. Introduction: The Evolution of Security Management
Information security has shifted over the past thirty years, evolving from a technically focused, back-office role to a core component of enterprise risk management and corporate governance. It no longer merely lists controls; it establishes the philosophical, legal, and ethical frameworks essential for managing security as a business function. As organisations confront an increasingly unpredictable threat landscape marked by state-sponsored cyberwarfare, complex supply chain vulnerabilities, and rigid regulatory requirements, security professionals must shift from being purely technologists to strategic risk advisors.
Modern security practitioners must navigate a complex ecosystem in which the confidentiality, integrity, and availability (CIA) of data are essential to operational viability. This demands a nuanced understanding of how security aligns with business strategy, the legal implications of data management, and the rigorous application of due diligence. By combining insights from global frameworks such as ISO/IEC 27001 and NIST SP 800-series publications, this analysis gives you a roadmap to build a security posture that supports, not hinders, your growth goals.
2. Security Governance and Strategic Alignment
Security governance is the set of responsibilities and practices exercised by the board and executive management to provide strategic direction, ensure objectives are achieved, manage risks appropriately, and verify that the enterprise's resources are used responsibly. It is the bridge that connects the technical implementation of security controls to the enterprise's strategic goals. Without effective governance, security initiatives often become misaligned with business needs, leading to resource wastage and unmitigated risk.6
2.1 The Philosophy of Business-Aligned Security
The primary directive for any security practitioner is to ensure that the security function enables the business. Historically, security departments were often perceived as the "department of no," focused exclusively on risk avoidance. However, in the modern digital economy, risk is an inherent component of value creation. Therefore, governance must shift toward "business-aligned security," in which security strategies are derived directly from, and support, business goals.8
If a business strategy involves rapid expansion into new international markets via cloud services, the security strategy must prioritise cloud security governance, identity federation, and scalable compliance monitoring. It should not block cloud adoption due to inherent risks, but rather implement controls that bring those risks within the organisation's appetite. This alignment requires integrating cybersecurity into strategic planning processes, including mergers and acquisitions (M&A), product development lifecycles, and supply chain selection.6 This "shift left" approach in governance ensures that security considerations are addressed during the design phase of business initiatives—often referred to as "Security by Design"—thereby reducing the cost and complexity of retrofitting controls later.
Furthermore, we must articulate the value of security investments in business terms. Instead of reporting on technical metrics such as "vulnerabilities patched" or "firewall packets dropped," governance reporting should focus on business outcomes: protecting revenue streams, preserving brand reputation, ensuring operational continuity, and avoiding regulatory fines. This translation of technical risk into business risk is the essence of strategic alignment.
2.2 Roles and Responsibilities in Governance
Effective governance requires a clearly defined organisational structure where roles, responsibilities, and decision-making authorities are unambiguous. The separation of duties and the establishment of clear reporting lines are critical to prevent conflicts of interest and ensure accountability.3
2.2.1 Senior Management and the Board of Directors
The ultimate responsibility for an organisation's security posture and liability lies with Senior Management and the Board of Directors. They are the fiduciaries responsible for defining the organisation's risk appetite—the amount of risk the organisation is willing to accept in pursuit of its objectives. They must practice Due Care by ensuring that the organisation acts legally and prudently. While they can delegate the authority to implement security measures, they can never delegate the responsibility for them. They approve high-level security policies and ensure that the security program is adequately funded and resourced.3
2.2.2 Data Roles: Owner, Custodian, and User
The governance of data requires a specific hierarchy of responsibility to ensure accountability.
Data Owner: Typically a senior business executive or manager who bears ultimate responsibility for a specific dataset or information asset. The Data Owner is liable for protecting the data and must determine its classification level (e.g., Confidential, Secret, Top Secret) based on the data's value to the organisation and the impact of its loss. They define the business requirements for access and authorise user privileges in line with the principle of Least Privilege.
Data Custodian: Typically, an IT professional or system administrator responsible for implementing the technical controls defined by the Data Owner. They perform day-to-day data security maintenance, including running backups, applying encryption, configuring access control lists (ACLs), and managing data retention and disposal. They act as the "hands" of the Data Owner.
Data User: Any employee, contractor, or third party who accesses data to perform their job duties is a Data User. They have a responsibility to adhere to the organisation's security policies, such as Acceptable Use Policies (AUP), and to handle data in accordance with its classification. They must exercise Due Care in their daily operations, such as locking workstations and not sharing passwords.
2.3 Security Control Frameworks
To manage security consistently and measurably, organisations adopt security control frameworks. These frameworks provide a structured methodology for identifying risks, selecting controls, and auditing compliance. They allow organisations to benchmark their security posture against industry best practices.
Table 1: Comparison of Major Security Governance Frameworks
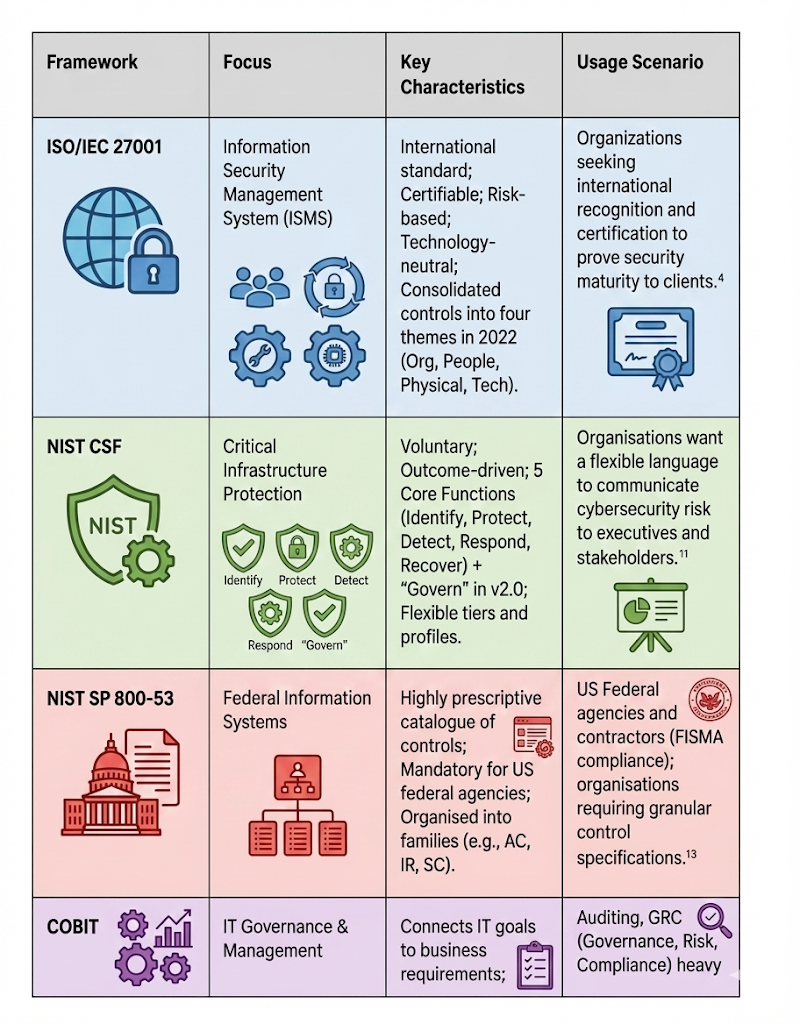
The choice of framework often depends on the organisation's industry and regulatory environment. For example, a US defence contractor must align with NIST SP 800-53, while a global SaaS provider might prioritise ISO 27001 certification to demonstrate trust to international customers.
The NIST Cybersecurity Framework (CSF) has gained massive traction in the private sector due to its accessible language and its organisation of security activities into functions that non-technical executives can understand: Identify, Protect, Detect, Respond, Recover, and the recently added Govern function, which emphasises the role of leadership in security.
2.4 Due Care vs. Due Diligence
Central to governance and legal liability are the concepts of Due Care and Due Diligence. These terms, while often used interchangeably in casual conversation, have distinct legal and operational meanings in the context of information security. Understanding the difference is vital to protecting the organisation from negligence claims.
Due Diligence is the investigative, research, and planning phase. It is the process of "doing your homework" before deciding or entering into an agreement. It asks, "Do we know what we need to know?" In security, Due Diligence involves activities such as conducting a risk assessment, performing background checks on new hires, researching the security posture of a potential third-party vendor, or analysing the implications of a new regulation, such as GDPR. It is the act of gathering the necessary intelligence to make an informed decision.
Due Care, by contrast, is the operational, implementation, and action phase. It is the act of doing what a reasonable and prudent person would do given the same circumstances (the "Prudent Person Rule"). If Due Diligence identifies a risk (e.g., a critical vulnerability in a web server), Due Care is patching that vulnerability. It involves ongoing maintenance of the security posture, including monitoring logs, enforcing policies, and training employees. Failure to practice Due Care is often the legal definition of negligence. In a lawsuit following a data breach, the court will ask whether the organisation exercised due care in protecting the data.
To synthesise the relationship: Due Diligence identifies the risks and the necessary controls; Due Care is the implementation and maintenance of those controls. You cannot effectively practice Due Care without the foundation of Due Diligence.
3. The Legal and Regulatory Compliance Landscape
Security professionals operate within a complex web of legal and regulatory requirements. Ignorance of the law is not a defence; therefore, practitioners must understand the various categories of law, intellectual property protections, and the evolving landscape of privacy regulations.
3.1 Categories of Law and Liability
The legal system typically classifies laws into three primary categories relevant to information security, each with different standards of proof and potential penalties.
Criminal Law: This body of law deals with conduct that is considered harmful to society as a whole. The government prosecutes it. Examples include the Computer Fraud and Abuse Act (CFAA) or laws against cyberstalking. The standard of proof is high: "Beyond a reasonable doubt" (near 100% certainty). Penalties involve imprisonment, fines paid to the state, and probation. The goal is punishment and deterrence.
Civil (Tort) Law: This addresses disputes between private parties (individuals or organisations) resulting in injury or loss. Examples include breach of contract, negligence (failure of Due Care), or intellectual property disputes. The standard of proof is lower: "Preponderance of the evidence" (more likely than not, >50%). Remedies are usually financial: Compensatory damages (to repay actual loss), Punitive damages (to punish the offender), or Statutory damages (set by law). The goal is to make the victim whole.
Administrative (Regulatory) Law: This involves rules and regulations enforced by government agencies (e.g., FDA, SEC, FTC) to govern specific industries. Examples include HIPAA and banking regulations. The standard of proof is often "preponderance of the evidence." Penalties include administrative fines, license revocation, or other sanctions. Corporate officers can be held personally liable for failures (e.g., under the Sarbanes-Oxley Act).
3.2 Intellectual Property (IP) Protection
Intellectual property is a critical asset for most modern organisations. Security controls must be designed to prevent the theft or unauthorised dissemination of IP.
Patent: A grant of property rights to an inventor for an invention (machine, process, manufacture). It grants the owner the right to exclude others from making, using, or selling the invention for a set period (typically 20 years). To obtain a patent, the invention must be novel and valuable, and the details must be publicly disclosed. Once the patent expires, the invention enters the public domain.
Copyright: Protects the expression of an idea, not the idea itself. It covers literary works, musical compositions, and notably, software code. Protection is automatic upon creation, though registration provides legal benefits. It typically lasts for the author's life plus 70 years (or 95 years for corporations). It protects against unauthorised copying and distribution.
Trademark: Protects words, names, symbols, sounds, or colours used to distinguish goods and services (branding). The goal is to prevent consumer confusion. Trademarks can be renewed indefinitely as long as they are in use and defended. An organisation must actively protect its trademark to avoid "abandonment" or "genericide".
Trade Secret: Proprietary business information that provides a competitive edge (e.g., the Coca-Cola formula, Google search algorithm, customer lists). Unlike patents, trade secrets are not registered. Protection relies entirely on keeping the information secret. If a trade secret is disclosed (even accidentally), the protection is lost forever. Security controls like NDAs, access controls, and encryption are the primary means of protecting trade secrets.
3.4 Privacy Protection and Transborder Data Flows
Privacy is the right of individuals to control the use and dissemination of their personal data. The landscape of privacy law has shifted dramatically, mainly driven by the European Union.
3.4.1 OECD Privacy Guidelines
In 1980, the Organisation for Economic Cooperation and Development (OECD) established eight guidelines that serve as the foundation for most modern privacy frameworks, including GDPR 27:
Collection Limitation: Data should be obtained lawfully and with consent.
Data Quality: Data should be relevant, accurate, and up to date.
Purpose Specification: The purpose for collection must be specified at the time of collection.
Use Limitation: Data should not be used for other purposes without consent.
Security Safeguards: Reasonable security controls must protect data.
Openness: There should be transparency regarding data practices.
Individual Participation: Individuals have the right to access and challenge their data.
Accountability: Data controllers are accountable for complying with these measures.
3.4.2 General Data Protection Regulation (GDPR)
The GDPR is the most comprehensive privacy law globally, applying to any organisation that processes the data of EU residents, regardless of the organisation's location (extraterritoriality). Key provisions include:
Consent: Must be explicit, informed, and freely given.
Data Subject Rights: Right to erasure ("Right to be Forgotten"), data portability, access, and rectification.
Breach Notification: Mandatory notification to the supervisory authority within 72 hours of becoming aware of a breach.
Penalties: Fines up to €20 million or 4% of global annual turnover, whichever is higher.32
3.4.3 US-EU Data Transfer Mechanisms
The transfer of personal data from the EU (which has strict privacy laws) to the US (which lacks a federal omnibus privacy law and allows broad intelligence surveillance) has been legally contentious. Several frameworks have been negotiated and subsequently invalidated by the Court of Justice of the European Union (CJEU):
Safe Harbour: Invalidated in 2015 (Schrems I) due to US surveillance concerns.
Privacy Shield: Invalidated in 2020 (Schrems II) for similar reasons regarding lack of redress for EU citizens.
EU-U.S. Data Privacy Framework (DPF): The current mechanism, approved in July 2023. It introduced a Data Protection Review Court (DPRC) to address redressal issues. While it currently allows data flow, it faces ongoing legal challenges from privacy activists. However, the EU General Court dismissed initial challenges in late 2025.34 Organisations utilise this framework by self-certifying with the US Department of Commerce.36
5. Risk Management Concepts and Frameworks
Risk management is the iterative process of identifying, assessing, and responding to risks to keep them within acceptable levels.
5.1 Risk Assessment Methodologies (NIST SP 800-30)
NIST SP 800-30 Rev 1 (Guide for Conducting Risk Assessments) defines risk assessment as a four-step process 5:
Please prepare the assessment's context, scope, purpose, and constraints.
Conduct: Identify threat sources (adversarial, accidental, structural, environmental) and threat events. Identify vulnerabilities and predisposing conditions. Determine the Likelihood of occurrence and the Impact (Magnitude of harm). Risk = Likelihood × Impact
Please share the results with decision-makers to support risk response.
Maintain: Monitor risk factors over time (continuous monitoring) to account for environmental changes.
5.2 Quantitative Risk Analysis
Quantitative analysis attempts to assign objective monetary values to risk components. This enables a cost-benefit analysis of security controls.
Key Metrics:
Asset Value (AV): The financial worth of the asset (e.g., $100,000 database).
Exposure Factor (EF): The percentage of loss a realised threat would cause (e.g., a fire might destroy 60% of the server facility).
-
Single Loss Expectancy (SLE): The monetary loss from a single occurrence of the threat.
SLE = AV x EF
Annualised Rate of Occurrence (ARO): The estimated frequency of the threat per year (e.g., once every 10 years = 0.1; twice a year = 2.0).
Annualised Loss Expectancy (ALE): The expected yearly financial loss from this risk. ALE = SLE \times ARO
Cost-Benefit Analysis: To determine whether a safeguard (countermeasure) is financially viable, the safeguard's cost must be less than the risk it mitigates.
5.3 Risk Response Strategies
Once risk is analysed, senior management must decide how to handle it. There are four primary strategies:
Risk Avoidance: discontinuing the activity that causes the risk (e.g., shutting down a vulnerable legacy server).
Risk Mitigation (Reduction): Implementing controls to lower the likelihood or impact (e.g., installing a firewall).
Risk Transfer (Sharing): Passing the financial impact to a third party (e.g., purchasing cyber insurance).
Risk Acceptance: Acknowledging the risk and choosing to operate with it, usually because the cost of mitigation exceeds the potential loss. This must be formally signed off by senior management.
5.4 The Risk Management Framework (RMF) - NIST SP 800-37
The NIST RMF (SP 800-37 Rev 2) provides a lifecycle approach to security authorisation. It integrates security, privacy, and supply chain risk management. It consists of seven steps :
1. Prepare: Essential organisational and system-level preparation.
2. Categorise: Categorise the system and information based on impact (FIPS 199).
3. Select: Select the baseline security controls (NIST SP 800-53).
4. Implement: Deploy the controls and document their implementation.
5. Assess: Determine if controls are correct, operating as intended, and producing desired outcomes (NIST SP 800-53A).
6. Authorise: The Authorising Official (AO) grants the Authority to Operate (ATO) based on the risk.
7. Monitor: Continuously monitor the system and controls for effectiveness.
9. Conclusion
Risk management is the strategic core of information security, encompassing legal compliance, ethics, financial risk, and governance. Security professionals must translate threats into business risks (ALE/SLE), navigate privacy laws (GDPR/DPF), and build resilient architectures (RMF/BCP). When we integrate these elements, they support the enterprise mission.