An Analysis of Governance, Risk, and Compliance
The contemporary landscape of information security has evolved from a technical support function to become a cornerstone of organisational strategy, enterprise risk management, and operational resilience. As organisations navigate an increasingly volatile threat landscape, stringent regulatory requirements, and complex digital ecosystems, the role of security leadership has shifted.
1.1 Establish Security’s Role in Organisational Culture, Vision, and Mission
The efficacy of an information security program is rarely determined solely by its technical controls, such as firewalls, intrusion detection systems, and encryption protocols, which are commodities available to all. Instead, success is contingent upon the program's alignment with the organisation's core identity. Security leaders must articulate a clear vision and mission that resonates with broader business objectives, ensuring that security is perceived not as a hindrance to operations but as a strategic enabler of trust and innovation.
Defining Information Security Program Vision and Mission
A vision statement is aspirational and future-oriented. It outlines the desired future state of the organisation's security posture, answering the fundamental question: "What do we want to become?" It serves as a "north star," guiding long-term decision-making and inspiring the security team and the broader organisation toward a common future. For example, a global financial institution might craft a vision statement declaring an intent "To be the global benchmark for trust and resilience in the financial sector, where security is invisible yet omnipresent." This statement sets a high bar, encouraging the team to strive for excellence and innovation over a 5- to 10-year horizon. It is not about what is achievable today, but what is possible tomorrow.
In contrast, a mission statement is operational and present-focused. It defines the program's current purpose, its scope of operations, and its primary value proposition. It addresses the questions: "Why do we exist?" and "What do we do today?"
A robust mission statement for a healthcare provider’s security program might read: "To protect the confidentiality, integrity, and availability of patient data through proactive risk management and resilient architecture, ensuring the uninterrupted delivery of life-saving care". While the vision paints a picture of the future, the mission focuses on the execution required to achieve it.
The process of crafting these statements requires deep introspection. Key questions include "Who do we serve?" (e.g., patients, customers, shareholders) and "What makes our approach unique?" If a mission statement is too vague, such as "We secure data", it fails to provide the necessary strategic guidance or differentiation. Effective statements are concise, memorable, and explicitly linked to the organisation's unique value proposition.
Aligning Security with Organisational Goals, Objectives, and Values
Strategic alignment is the mechanism by which security initiatives support the broader business. Security cannot operate in a vacuum; it must be aligned with the organisation's goals, objectives, and values. Misalignment often manifests as friction: if a business aims to be the "fastest to market" with new software features, a security programme that imposes week-long manual code reviews creates strategic drag. Instead, the security mission must adapt to support "secure speed" through automation, CI/CD integration, and DevSecOps principles.
Alignment ensures that security investments are prioritised based on their contribution to business success. For instance, if an organisation's strategic goal is to expand into the European market, the security programme must prioritise GDPR compliance, data residency solutions, and EU-specific privacy controls. This alignment enables security functions to position themselves as strategic partners rather than cost centres. By mapping security objectives (e.g., "Achieve ISO 27001 certification") directly to business goals (e.g., "Enter enterprise markets requiring verified security"), the CISO demonstrates tangible business value.
Furthermore, security values must mirror organisational values. If an organisation prizes "transparency," the security team cannot operate as a "black box." It must share metrics, openly admit failures, and communicate transparently about risks.
Defining Security’s Relationship with Overall Organisation Processes
Security must be integrated into the fabric of organisational processes, from human resources and legal to operations and product development. This integration ensures that security controls are "baked in" rather than "bolted on".
Human Resources (HR): Security interacts with HR throughout the entire employee lifecycle. During hiring, security mandates background checks and screening. During employment, HR enforces acceptable use policies and ensures compliance with security training. During offboarding, the two functions coordinate to revoke access and recover assets immediately, preventing insider threats or data leakage.7
Legal and Compliance: Legal defines the regulatory landscape (what laws apply), and Security provides the technical controls and evidence required to meet those obligations (e.g., HIPAA, SOX, GDPR). Legal also relies on security for eDiscovery and forensics during litigation.
IT and Operations: IT typically focuses on availability, performance, and feature delivery, while security focuses on confidentiality, integrity, and risk management. Tensions often arise between patching windows (uptime vs security) and access controls (usability vs security). Precise definitions of roles—such as who patches servers and who scans for vulnerabilities—are essential for resolving these conflicts.
The "CIA Triad"—Confidentiality, Integrity, and Availability—serves as the universal language for defining these relationships.
Confidentiality: Ensures data is accessible only to authorised entities.
Integrity: Guarantees data accuracy and reliability.
Availability: Ensures systems function when needed.
Defining the Relationship Between Organisational Culture and Security
Organisational culture—the shared values, beliefs, and behaviours of the workforce—fundamentally dictates the effectiveness of a security program. A strong "security culture" is one where every employee, regardless of role, understands their contribution to protecting the organisation. Security leaders must assess the existing culture to identify gaps between the "current state" and the "aspired state".
Culture can be categorised by how it rewards or punishes behaviour:
Behaviours: What actions are rewarded? If an employee bypasses security controls to meet a deadline and is praised for "speed" or "heroics," the culture implicitly undermines security. Conversely, if reporting a potential phishing attempt is celebrated, the culture reinforces vigilance.
Relationships: How do departments interact? Strong cross-functional relationships foster better incident response. If the network and security teams have a collaborative relationship, they can contain a breach faster than if they are siloed and adversarial.
Attitudes: Is security seen as the "Department of No" or a business enabler? A positive attitude transfer philosophy suggests that if management cares for staff, staff will care for the organisation's assets. Leaders who demonstrate care and concern create an environment where employees feel a personal stake in protecting the company.13
1.2 Align Security Program with Organisational Governance
Governance is the system by which the security program is directed and controlled. It is distinct from management; governance determines the "what" and "why" (strategic direction, risk appetite, and oversight), while management handles the "how" (execution and operations).
Identifying and Navigating Organisational Governance Structure
Security governance establishes the framework for decision-making, accountability, and oversight. It ensures that security activities align with the organisation's risk tolerance and business objectives. A robust governance framework, such as COBIT 2019 or NIST SP 800-53, provides a structured approach to managing these complexities.
Effective governance requires identifying where security fits within the corporate hierarchy. The Chief Information Security Officer (CISO) 's reporting line significantly affects the program's independence and authority.
Reporting to the CIO: Historically common, but can create a conflict of interest where security takes a backseat to IT operational performance or budget.
Reporting to the CEO/Board: Ideally, the CISO reports to a risk committee, the CEO, or the General Counsel to ensure independence from IT and a direct line to executive decision-makers.
Two primary forces drive governance:
Internal Governance: Driven by internal objectives, risk appetite, corporate bylaws, and business strategy.
External Governance: Driven by laws, regulations (e.g., GDPR, CCPA), and industry standards (e.g., PCI DSS) that mandate specific controls and oversight mechanisms.14
Governance bodies typically include a Security Steering Committee. This committee comprises senior executives from various business units (HR, Legal, Finance, Ops). It is responsible for reviewing security strategies, approving central budgets, and resolving conflicts between security requirements and business priorities.
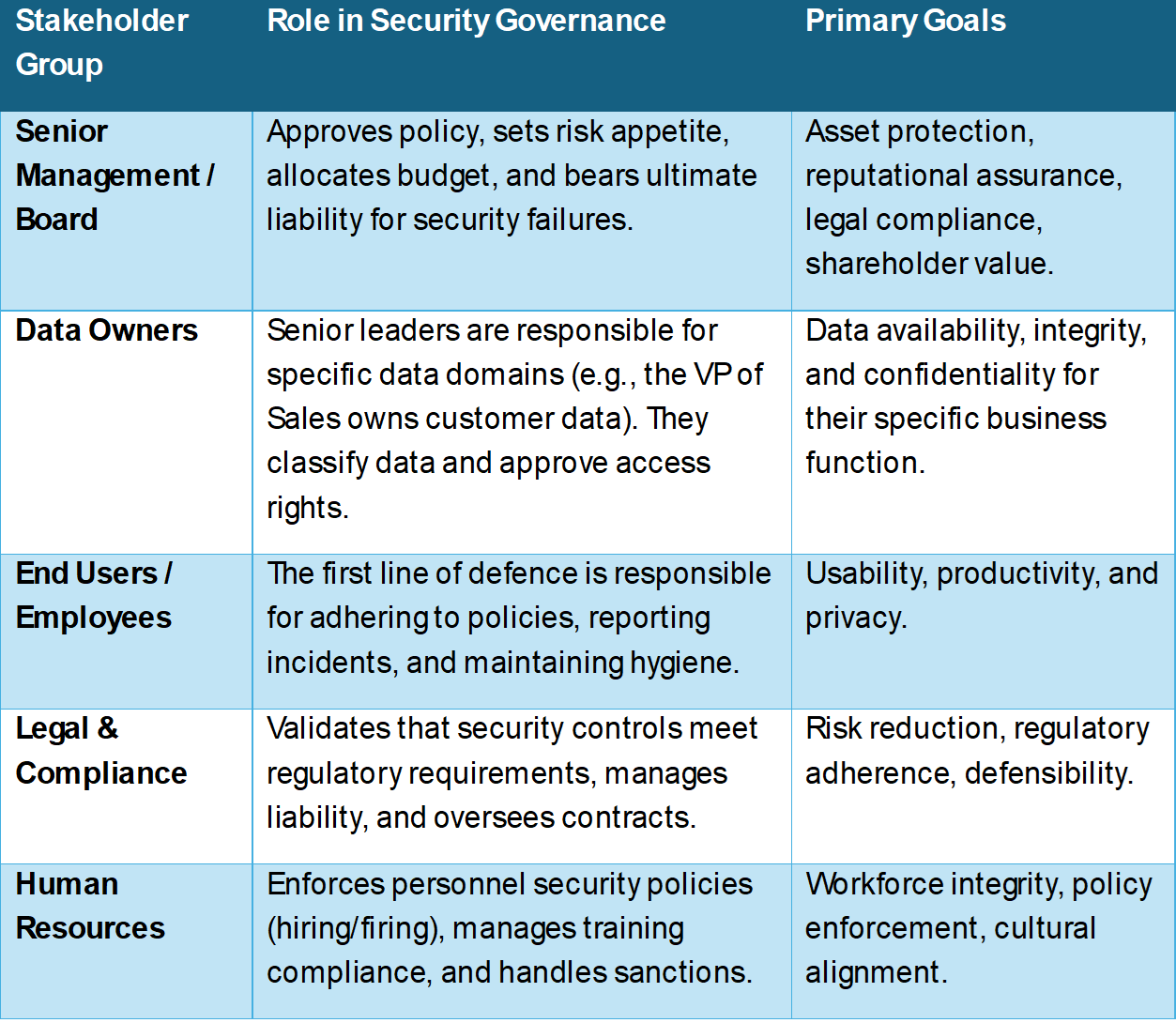
Verifying and Validating Roles of Key Stakeholders
Stakeholders are individuals or groups who affect, or are affected by, the security program. Identifying them and validating their roles is crucial for obtaining buy-in and ensuring accountability.
Validating Sources and Boundaries of Authorisation
Authorisation refers to the legitimate power to make decisions and enforce policies. Security leaders must validate the sources of this authority to ensure their mandates are respected and legally defensible.
Charter: A Security Charter is a formal document signed by the CEO or Board that delegates authority to the security function. It defines the CISO's mandate to act.
Policy: Approved security policies serve as the organisation's codified laws. Once signed by executive leadership, they provide the authority to enforce rules.
Boundaries: Security must respect the limits of its authority to maintain trust and legality. For example, security teams may be authorised to monitor corporate email for malware (authorised) but are likely restricted from reading personal emails unless specific legal criteria and HR approvals are met (boundary). Understanding and documenting these boundaries prevents overreach and privacy violations.
Advocating and Obtaining Organisational Support for Security Initiatives
Support from top management is the single most critical factor for a successful security program. Without "tone from the top," policies are ignored, exceptions become the norm, and budgets are cut.
Advocacy strategies include:
Business Case Development: Presenting security initiatives not as technical upgrades but as business enablers. Leaders should use metrics such as Return on Security Investment (ROSI) to justify costs and show how a control reduces potential loss.
Risk Translation: Translating technical risks into business language. Instead of reporting "SQL injection vulnerability on Server X," the CISO should report "Potential loss of 50% of customer revenue due to database downtime and data theft".
Steering Committees: Using the steering committee to gain consensus. When the CFO and General Counsel agree on a security initiative, it gains organisational legitimacy and is harder for other units to resist.
Executive Sponsorship: Securing a specific C-level champion (e.g., the CFO or COO) who can advocate for security in closed-door board meetings where the CISO may not be present.
1.3 Define and Implement Information Security Strategies
A security strategy is a high-level roadmap that outlines how the organisation will achieve its security vision over a 3-5 year horizon. It bridges the gap between current capabilities and future needs, ensuring the program evolves with the threat landscape.
Identifying Security Requirements from Organisational Initiatives
Security requirements must be derived directly from the business's strategic plan. If the organisation plans to transform and move to the cloud digitally, the security strategy must pivot to Cloud Security Posture Management (CSPM) and CASB (Cloud Access Security Broker) solutions. If the plan involves growth through Mergers and Acquisitions (M&A), the security strategy must focus on rapid assessment, due diligence, and network integration frameworks.
Key inputs for identifying requirements include:
Business Impact Analysis (BIA): A formal process that identifies critical business processes and the impact of their disruption. This helps prioritise which assets need the strongest protection.
Threat Landscape Assessment: Understanding the specific adversaries (e.g., nation-states, cybercriminals, hacktivists) targeting an industry.
Regulatory Analysis: Identifying new or upcoming laws (e.g., AI regulation, SEC disclosure rules) that will require control changes.
Evaluating Capacity and Capability to Implement Security Strategies
Before launching a strategy, leaders must assess the organisation's ability to execute it. This prevents the "strategy-execution gap."
Capacity: Do we have enough people, time, and budget? If the strategy requires 24/7 monitoring, do we have the headcount for three shifts?.
Capability: Do we have the right skills and technology? Does the current staff know how to secure Kubernetes containers, or do we need training/consultants?.
A Gap Analysis compares the "Current State" (what we can do now) with the "Desired State" (what the strategy requires). For instance, if the plan calls for a zero-trust model but the network is flat and legacy-based, there is a significant capability gap that must be addressed through infrastructure upgrades or outsourcing.
Prescribing Security Architecture Design
A robust security architecture must underpin the strategy. This includes selecting the frameworks and models that will guide technical implementation.
Defence in Depth: Implementing multiple layers of controls (firewalls, endpoint protection, user training, data encryption) so that if one fails, others remain to stop the attack.
Zero Trust Architecture: Moving away from perimeter-based security ("trust but verify") to a model where every access request is authenticated, authorised, and encrypted, regardless of user location or device ("never trust, always verify").
Secure by Design: Integrating security into the architecture of IT projects from the very start, rather than retrofitting it later. This is cheaper and more effective.
Frameworks: Utilising standard architectural frameworks like SABSA (Sherwood Applied Business Security Architecture) or TOGAF (The Open Group Architecture Framework) to ensure comprehensive coverage.
Managing Implementation of Security Strategies
Implementation involves converting the high-level strategy into tactical projects and operational tasks.
Roadmaps: Developing a phased timeline of initiatives (e.g., Year 1: MFA rollout; Year 2: DLP implementation; Year 3: Zero Trust pilots).
Resource Allocation: Assigning budget and personnel to specific projects within the portfolio.
Change Management: Managing the cultural and procedural changes required by new security controls. This is often the most challenging part, as security changes (such as 2FA) disrupt established workflows and generate user resistance.
Reviewing and Maintaining Security Strategies
Strategies are not static. They must be reviewed periodically (e.g., annually) or in response to significant triggers (e.g., a major industry breach, new regulation, or leadership change).
Performance Measurement: Using metrics to track progress against strategic goals (e.g., "Have we achieved 100% MFA coverage as planned?").
Environmental Scanning: Continuously monitoring the threat landscape and technology trends (e.g., rise of Generative AI) to ensure the strategy remains relevant. If AI changes the threat model, the strategy must adapt.
1.4 Define and Maintain Security Policy Framework
The policy framework is the hierarchical set of documents that define the organisation's rules, requirements, and procedures. It is the bureaucratic backbone of the security program, providing the "law" that governs behaviour.
Determining Applicable External Standards, Laws, and Regulations
The first step in policy creation is understanding the external obligations. These dictate the minimum baseline for internal policies.
Laws/Regulations: GDPR (EU), CCPA/CPRA (California), HIPAA (Healthcare), SOX (Public Companies), GLBA (Financial).
Industry Standards: PCI DSS (Credit Cards), NERC CIP (Energy).
Frameworks: NIST Cybersecurity Framework (CSF), ISO 27001, CIS Controls, COBIT 2019.
For example, if HIPAA requires "encryption of data at rest," the internal Data Protection Policy must mandate encryption across all systems that store health data.
Determining Data Classification and Protection Requirements
Data classification is the process of categorising data based on its sensitivity and value to the organisation. This allows for efficient allocation of security resources—protecting the "crown jewels" more heavily than public data. Common classification levels include:
Public: No harm if disclosed (e.g., marketing materials, press releases).
Internal Use: Low harm if disclosed (e.g., organisational charts, internal memos).
Confidential: Moderate harm (e.g., contracts, pricing strategies, employee salaries).
Restricted/Secret: Severe harm (e.g., customer PII, trade secrets, source code, private keys).
Protection requirements are then mapped to these levels. "Restricted" data might require encryption at rest, MFA for access, and DLP monitoring, while "Public" data requires only integrity checks.
Establishing Internal Policies
Policies are high-level statements of intent signed by senior management. They explain what must be done and why, but generally not how.
Information Security Policy: The overarching document authorising the security program and defining its scope.
Acceptable Use Policy (AUP): Defines how employees can use corporate assets (internet, email, devices).
Access Control Policy: Defines the principles for granting and revoking access (e.g., least privilege, need-to-know).
Data Classification Policy: Defines the schema and handling requirements for data.
Effective policies must be:
Clear and Concise: Written in plain language to be understood by all employees, avoiding jargon where possible.
Enforceable: Do not create rules that cannot be monitored or enforced (e.g., "Do not look at the screen for too long").
Aligned with Risk: The policy's strictness should match the level of risk to the organisation.
Advocating and Obtaining Organisational Support for Policies
Policies without support are merely paper. Security leaders must "sell" policies to stakeholders to ensure adoption.
Stakeholder Review: Involve HR, Legal, and Operations in the drafting process. If Operations feels a policy makes their job impossible, they will ignore it. Co-authoring builds buy-in.
Executive Sign-off: Having the CEO or Board sign the policy sends a powerful message of importance and endorsement.
Communication: Explaining the "why" behind the policy to employees, rather than just the "what." People are more likely to comply if they understand the rationale (e.g., "This password policy protects your payroll data").
Developing Procedures, Standards, Guidelines, and Baselines
The policy hierarchy breaks down high-level intent into actionable steps:
Policies: High-level intent (Mandatory). "All passwords must be strong."
Standards: Specific technical requirements (Mandatory). "Passwords must be at least 12 characters, complex, and changed every 90 days."
Procedures: Step-by-step instructions (Mandatory). "1. Open System Settings. 2. Click Change Password. 3. Enter new password..."
Guidelines: Best practices (Optional/Recommended). "Users should avoid using dictionary words or names of pets."
Baselines: Minimum security configurations for specific systems (e.g., CIS Benchmarks for Windows Server 2019). These are detailed technical settings applied to hardware and software.
Ensuring Periodic Review of the Security Policy Framework
Policies must be living documents. A "set it and forget it" approach leads to non-compliance as technology and business needs evolve.
Annual Review: Policies should be formally reviewed at least annually to ensure they are still relevant and compliant with new laws.
Trigger-Based Review: Updates are required after significant changes, such as adopting new technology (e.g., moving to the cloud, which requires updating the Access Control Policy to include cloud resources) or after a significant security incident that revealed a policy gap.
1.5 Manage Security Requirements in Contracts and Agreements
In a hyper-connected global economy, an organisation is often only as secure as its weakest vendor. Managing third-party risk is a critical domain of security leadership involving legal, operational, and technical due diligence.
Evaluating Service Management Agreements (SMAs)
Service Management Agreements (often part of SLAs) define the performance and security expectations between the organisation and a vendor. Security leaders must evaluate these agreements for:
Risk: Does the vendor introduce acceptable levels of risk? Does their access level match their business need?
Financial: Are the costs of security controls (e.g., dedicated firewalls, private cloud instances) explicitly included in the pricing?
Right to Audit: Does the contract allow the organisation to audit the vendor's security controls or review their third-party audits (e.g., SOC 2 Type II)?.
Governing Managed Services (Infrastructure, Cloud)
When outsourcing infrastructure (IaaS, PaaS, SaaS), the organisation retains the ultimate responsibility for data security under the Shared Responsibility Model. Governance involves:
Defining Responsibilities: Clearly mapping who does what. Who patches the OS? Who secures the data? In SaaS, the vendor does most of the work; in IaaS, the customer does.
Monitoring Performance: Ensuring the vendor meets security SLAs. This includes uptime (e.g., 99.9%), incident response times (e.g., notify within 1 hour), and patch turnaround (e.g., critical patches within 24 hours).
Managing Security Impact of Organisational Change (M&A, Outsourcing)
Organisational changes introduce massive risk.
Mergers & Acquisitions (M&A): The acquiring company inherits the target's vulnerabilities and threat actors. Due diligence must assess the target's security posture before the deal closes to identify "toxic" cyber assets or ongoing breaches. Post-merger integration requires careful segmentation until the target network is brought up to standard.
Outsourcing: Moving a function (e.g., payroll, customer support) to a third party requires strict contractual security controls to prevent data leakage. The risk is transferred operationally but retained reputationally.
Ensuring Regulatory Compliance in Contracts
Contracts must mandate compliance with relevant regulations to protect the organisation from liability.
Data Processing Agreements (DPAs): Required by GDPR. The vendor (Processor) must agree to process data only on instructions from the organisation (Controller), implement specific security measures, and assist with data subject rights.
HIPAA Business Associate Agreements (BAA): Required for healthcare vendors handling PHI. It mandates that the vendor protect health data to the same standard as the covered entity.
Breach Notification: Contracts must specify a strict timeline for the vendor to notify the organisation of a breach (e.g., within 24 or 72 hours). This is often shorter than the statutory requirement, allowing the organisation time to react and notify regulators.
Monitoring and Enforcing Compliance
Signing the contract is just the beginning. Continuous monitoring is required to ensure the vendor maintains their security posture.
Vendor Risk Management (VRM): Using tools and standard questionnaires (e.g., SIG, CAIQ) to periodically reassess vendor security (e.g., annually for high-risk vendors).
Scorecards: Tracking vendor performance against security KPIs and providing feedback.
Termination: If a vendor consistently fails to meet security requirements or suffers a major breach due to negligence, the contract must allow for termination for cause.
1.6 Manage Security Awareness and Training Programs
The "human firewall" is often the most vulnerable component of the security architecture. Awareness programs aim to change human behaviour to reduce risk, transforming employees from targets into sensors.
Promoting Security Programs to Key Stakeholders
To get funding and support for training, security leaders must promote the program's value.
Executive Buy-in: Showing leaders that training reduces the likelihood of costly breaches (e.g., ransomware starting from a phishing email). Demonstrating ROI through reduced incident counts.
Internal Marketing: Using posters, newsletters, "Security Champions" programs, and town halls to keep security top-of-mind and approachable
Identifying Needs and Implementing Training by Target Segment
One size does not fit all. Training must be tailored to the employee's role and risk profile.
All Employees: Basic hygiene (passwords, phishing recognition, physical security).
Developers: Secure coding practices (OWASP Top 10), DevSecOps tools, and threat modelling.
Executives: High-level threat trends, "whaling"/CEO fraud, and risk decision-making.
Privileged Users (Admins): Advanced technical security, insider threat awareness, and secure system administration.
Monitoring, Evaluating, and Reporting Effectiveness
Participation (completion rates) is a metric, but not a measure of effectiveness. Leaders must measure behaviour change.
Phishing Simulations: Sending fake phishing emails and measuring the "click rate" and "reporting rate." A decreasing click rate and increasing reporting rate indicate success. It is crucial to use these for education, not punishment.
Culture Surveys: Assessing employee attitudes toward security (e.g., "Do you feel comfortable reporting a mistake?").
Metrics such as "Mean Time to Report" (how quickly a user reports a suspicious email) are valuable KRIs. A fast reporting time allows the SOC to react quickly
1.7 Define, Measure, and Report Security Metrics
"You cannot manage what you cannot measure." Metrics provide the data needed to make informed risk decisions, justify budgets, and demonstrate program maturity.
Identifying Key Performance Indicators (KPI) and Key Risk Indicators (KRI)
It is vital to distinguish between performance and risk metrics.
-
KPI (Key Performance Indicator): Measures the security team's performance.
Examples: Percentage of systems patched within 30 days; Mean Time to Detect (MTTD); Mean Time to Resolve (MTTR); Percentage of staff completing training.
Focus: Historical performance, operational efficiency, and goal attainment
-
KRI (Key Risk Indicator): Measures the level of risk the organisation faces. It is an early warning system.
Examples: Number of unpatched critical vulnerabilities > 30 days old; Number of users with local admin rights; Volume of blocked malware attempts; Number of policy exceptions granted.
Focus: Future probability of adverse impact and risk exposure.
Associating Metrics to Risk Posture
Metrics must be contextualised. Reporting "10,000 firewall blocks" is a vanity metric that means little to the Board. Reporting "A 20% increase in targeted attacks against the finance department" is actionable risk intelligence 50
Risk Tolerance: KRIs should have thresholds linked to risk appetite. If a KRI exceeds a threshold (e.g., >5% of laptops unencrypted), it triggers an immediate response or escalation.
Using Metrics to Drive Improvements
Metrics drive the feedback loop for the security program.
Budget Justification: "Our MTTD is high because we lack automation. We need a budget for a SOAR tool to bring this metric down."
Process Improvement: If patch latency is increasing, the patching process needs review (e.g., is the maintenance window too short, or are tools failing?).
Board Reporting: Presenting high-level KRIs (e.g., "Cyber Risk Score" or "Maturity Level") to the Board to demonstrate the state of security and the return on investment.
1.8 Prepare, Obtain, and Manage Security Budget
Security is a business function that requires financial acumen. The CISO must manage a budget like any other executive, balancing cost, risk, and value.
Preparing and Securing Annual Budget
Budgeting involves estimating the costs of personnel, technology, and services.
Zero-Based Budgeting: Building the budget from scratch each year based on necessary activities, rather than just adding a percentage to last year's budget. This requires justifying every expense.
Risk-Based Budgeting: Allocating funds to the areas of highest risk. If the most significant risk is ransomware, the budget should prioritise backup, endpoint protection, and training.
-
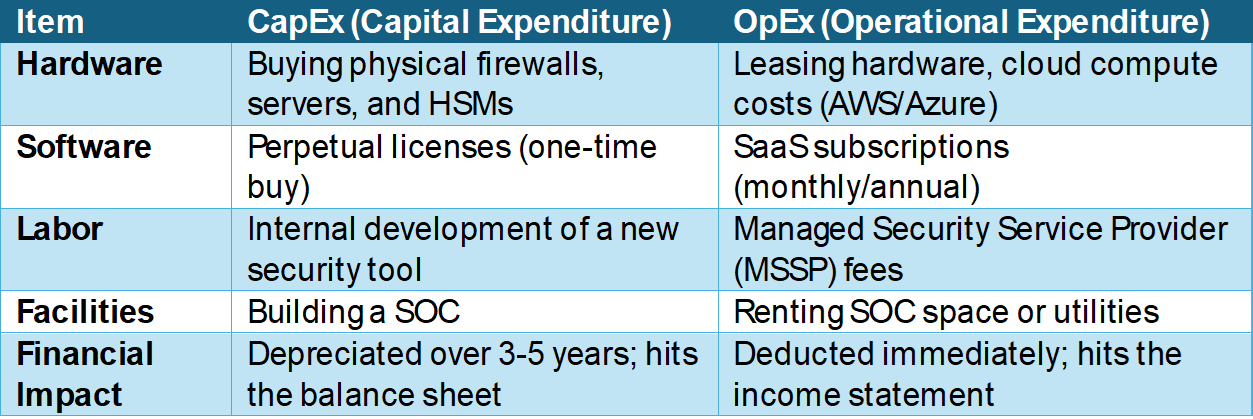
CapEx vs OpEx:
CapEx (Capital Expenditure): Upfront costs for long-term assets (e.g., buying servers, building a data centre, perpetual software licenses). These are depreciated over time.
OpEx (Operating Expenditure): Recurring costs (e.g., SaaS subscriptions, cloud fees, annual software maintenance, managed services). These are taken from the current year's revenue. The industry trend is moving toward OpEx due to cloud adoption and SaaS models.
Adjusting Budget Based on Evolving Risks
The threat landscape changes faster than the annual budget cycle. Leaders need flexibility.
Contingency Funds: Reserving 5-10% of the budget for unforeseen events (e.g., incident response retainer activation, urgent patch deployment).
Business Case: When asking for off-cycle budget (e.g., for a new tool to stop a zero-day exploit), the request must be framed as a business case (ROI, risk reduction, cost of inaction).
Managing and Reporting Financial Responsibilities
TCO (Total Cost of Ownership): Considering not just the purchase price, but the cost of implementation, training, maintenance, and support over the life of the asset.
ROI (Return on Investment): Hard to calculate for security (since security prevents loss rather than generating profit).
ROSI (Return on Security Investment): A modified formula: ROSI = (Risk Exposure x %Risk Mitigated) - Solution Cost)/(Solution Cost). This helps quantify the value of avoiding a breach.
1.9 Manage Security Programs
Program management involves coordinating multiple projects and operational activities to achieve strategic goals. It is the "glue" that holds the security function together.
Defining Roles and Responsibilities
Clear definitions prevent gaps and overlap in coverage.
CISO: Strategic leadership, board reporting, risk ownership.
Security Manager: Operational oversight, team management, tactical execution
Security Analyst: Technical execution (monitoring, incident response, vulnerability scanning).
Security Architect: Design and technical strategy, ensuring systems are secure by design.
Building Cross-Functional Relationships and Resolving Conflicts
Security often conflicts with other departments (e.g., "Security vs Usability" or "Security vs Speed").
CIO vs CISO: The classic conflict. CIO wants uptime/speed; CISO wants security/control. Resolution requires shared goals (e.g., "Secure Availability") and often separate reporting lines (e.g., CISO reporting to the CEO/CRO to avoid a conflict of interest).
-
Conflict Resolution: Techniques include active listening, focusing on business objectives (not technical arguments), and data-driven persuasion. The Thomas-Kilmann Conflict Mode Instrument:
Conflict Resolution: Techniques include active listening, focusing on business objectives (not technical arguments), and data-driven persuasion. The Thomas-Kilmann Conflict Mode Instrument, which has five response options, follows these five options.
-
1. Competing (Assertive, Uncooperative)
This is a power-oriented mode where an individual pursues their own concerns at the other person's expense.
Behaviour: "My way or the highway." It relies on power, rank, or ability to argue.
When to use: Effective for emergencies, situations requiring decisive action, or when implementing unpopular but necessary rules (e.g., enforcing a mandatory security patch immediately).
-
2. Accommodating (Unassertive, Cooperative)
The opposite of competing, this mode involves neglecting your own concerns to satisfy others'. It includes an element of self-sacrifice.
Behaviour: Yielding to another's point of view or obeying an order even when you prefer not to.
When to use: Useful when the issue is much more critical to the other person than to you, to build social credits for later issues, or when preserving harmony is vital.
-
3. Avoiding (Unassertive, Uncooperative)
In this mode, the person does not address the conflict. They do not pursue their own concerns or those of the other person.
Behaviour: Sidestepping the issue, postponing it for a better time, or withdrawing from a threatening situation.
When to use: Best for trivial issues, when you have no chance of winning, or when people need to cool down and regain perspective.
-
4. Collaborating (Assertive, Cooperative)
The opposite of avoidance, this mode involves working with the other party to find a solution that fully satisfies both parties' concerns.
Behaviour: Digging into an issue to identify the underlying needs of both individuals and finding a creative alternative.
When to use: Ideal when both sets of concerns are too important to compromise, such as when merging security requirements with a critical new business product.
-
5. Compromising (Intermediate Assertiveness and Cooperativeness)
The goal here is to find an expedient, mutually acceptable solution that partially satisfies both parties.
Behaviour: "Splitting the difference," exchanging concessions, or seeking a quick middle-ground solution.
When to use: Useful when goals are moderately essential but not worth the disruption of more assertive modes, or as a backup when collaboration fails.
-
Integrating Security Controls into Organisation Processes
Security should be invisible processes where possible.
Change Management: Security must be a voting member on the Change Control Board (CCB) to review the security impact of IT changes before they are implemented.
Procurement: Security review must be a mandatory step in the purchasing process for new software or vendors to prevent "Shadow IT".
Project Management Office (PMO): Security gates and requirements should be standard templates in the PMO's project methodology.
1.10 Apply Product Development and Project Management Principles
Integrating security into the systems development lifecycle (SDLC) and projects is essential for "Secure by Design."
Incorporating Security Throughout the Lifecycle
Shift Left: Moving security activities (testing, review) to the early phases of development (Design/Code) rather than waiting for Testing/Deployment. This is significantly cheaper and safer, as fixing a design bug costs pennies compared to fixing it in production.
DevSecOps: Integrating security automation into the CI/CD pipeline. Security becomes code (e.g., automated SAST scans on commit), enabling developers to fix issues in real-time.
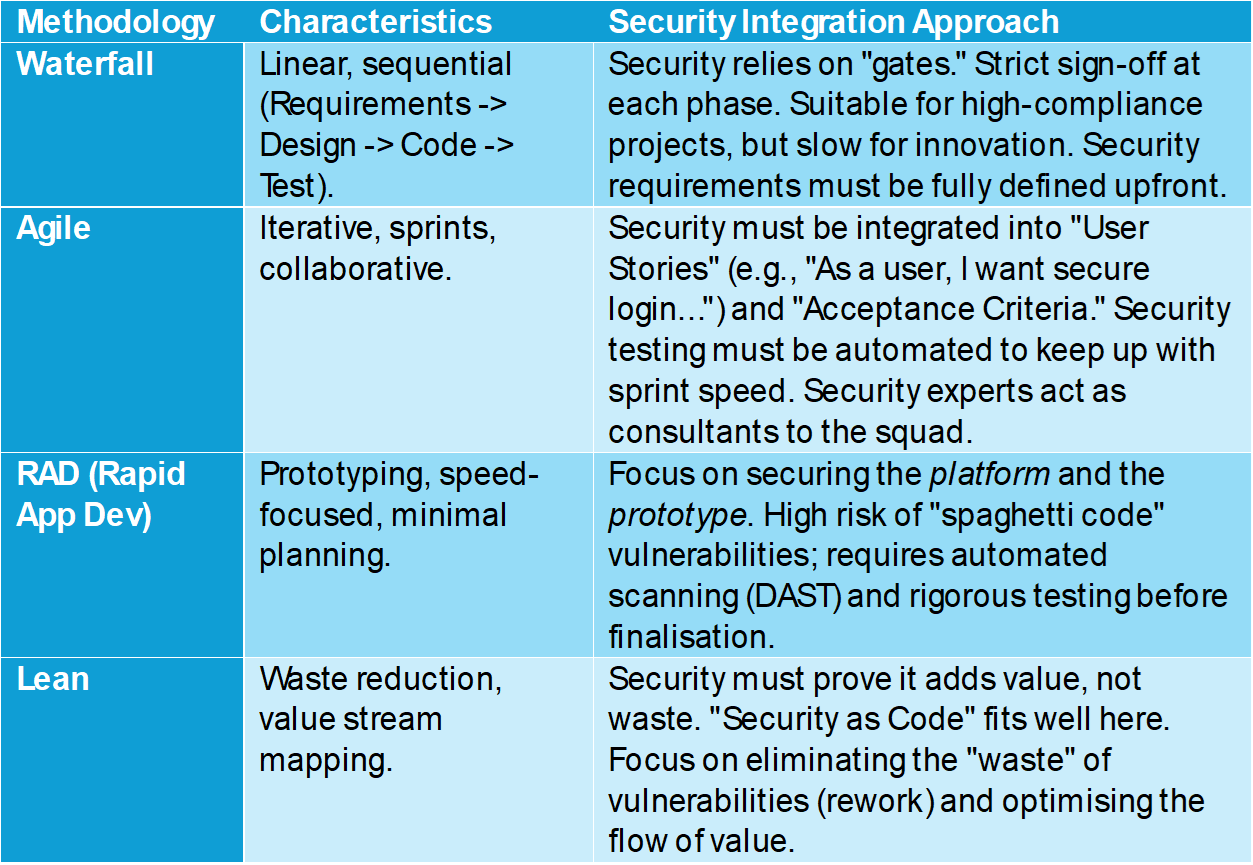
Identifying and Applying Applicable Methodology
Different methodologies require different security approaches.
Table 3: Security Integration in Project Methodologies
Analysing Project Scope, Timelines, Quality, and Budget
The "Project Management Triangle" (Scope, Time, Cost) applies to security as well.
Scope: Security requirements (e.g., encryption, logging) must be in the scope baseline. Adding them later is "scope creep" and expensive.
Quality: Security is a dimension of quality. Software with critical vulnerabilities is, by definition, low-quality software. Quality Assurance (QA) should include Security Assurance.
Budget: Security testing (penetration tests), tools (SAST/DAST), and training must be line items in the project budget (typically 5-10% of the total project cost).
Conclusion
Leadership and Operational Management act as the "brain" of the Information Security program. It is where intent is defined, resources are acquired, and rules are set. Without excellence in this domain, the technical controls in other domains will lack direction and sustainability.
Effective leadership requires a constant balancing act: balancing security with usability, risk with cost, and compliance with innovation. The tools provided in this agenda—from strategic roadmaps and governance frameworks to rigorous contract management and human-centric training—are the levers the CISO pulls to achieve this balance. By mastering these operational management principles, security leaders transform their function from a cost centre into a strategic asset that ensures the organisation's long-term resilience and success.